Posts Tagged hacking
You have 24 hours to build the future of music
Posted by Paul in data, fun, hacking, Music, music hack day, The Echo Nest on November 12, 2013

A Music Hack Day is unlike most other hackathons. There are no mega-prizes for the best hacks. There are no VCs wandering the hacker hallways trolling for the next startup. There are no briefs that describe the types of apps that you should build. Hackers don’t go to a Music Hack Day to win big prizes, or to launch their startup. Hackers go to Music Hack Days because they love music and they love to build stuff. At a Music Hack Day these passionate builders get to apply their talents to music, surrounded by like-minded peers and build their version of the future of music. The currency at a Music Hack Day is not money or VC attention, the currency is creativity. The Music Hack Day prize is knowing that you’ve built something cool enough to delight other music hackers.
So what happens at a Music Hack Day? How does it all work? What kind of hacks do people build? Read on to see exactly what happened at the Boston Music Hack Day 2013, held this last weekend.
Boston Music Hack Day

This weekend, hundreds of folks who are passionate about music and technology got together in Cambridge MA for Boston Music Hack Day 2013. The event was hosted at the Microsoft NERD – a wonderful facility that Microsoft makes available for all sorts of programmer events. Registration started at 9AM and by 10AM hackers were breakfasted and ready to go.
The event started off with some opening remarks by your truly, describing how a Music Hack Day works and how to have a successful event (meet other people, learn new stuff, build something, make sure you finish it, demo it and have fun).

Build Something! – key advice for a Music Hack Day

Hackers riveted by Paul Lamere’s opening remarks
Short technology presentations
Next up, organizations that had some sort of music technology such as an API or new gizmo that might be interesting to music hackers spent a few minutes talking about their technology. For many hackers, this was their first exposure to the music ecosystem – they don’t know what APIs are available for building apps so learning about music streaming APIs from companies like SoundCloud, Rdio and Spotify, and learning about all the music data available from APIs like The Echo Nest and the Free Music Archive is really important.

Matt talks about the Reverb.com API
There were a few interesting devices available for hackers at the event. Techogym brought a high tech treadmill with its own API hoping that music hackers would build music-related exercise apps. Muzik brought a set of headphones that are instrumented with accelerometers and other sensors allowing for apps to adapt to the actions of the listener.
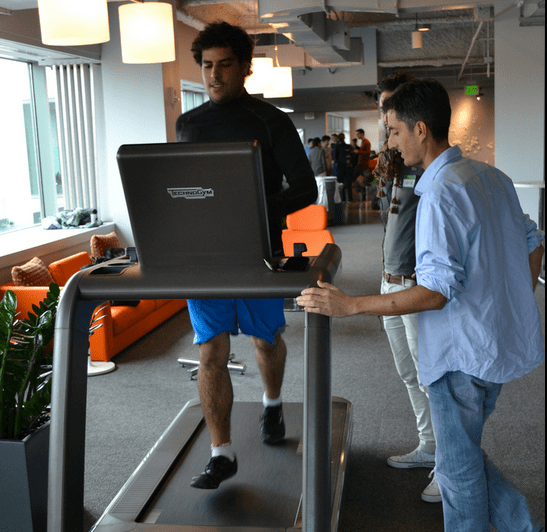
Hackers trying out the Technogym
Project Pitches
Sometimes hackers come to a Music Hack Day with ideas ready to go. Sometimes hackers come with their skills but no ideas. At the Project Pitch session, hackers had a minute to pitch their idea or to offer their skills. About 20 hackers braved the front of the room describing their idea or their skill set. One hacker described his project as help me with my homework (and yes, this hacker did find a teammate and they ultimately built a nifty hardware hack that satisfied the homework requirement too).

The homework as hack demo
Tech Deep Dives
Next up on the schedule were the Tech Deep dives. Organizations had a half-hour to give a deeper view of what their technology is capable of. Some hackers want to know more about how to do particular things with an API or technology. This is their opportunity to find out all about the nuts and bolts, to ask questions from the experts. The Tech Deep Dives are strictly optional – many hackers skip them and instead start forming teams, sharing ideas, initializing their repos and writing code.

Kevin does the Rdio API deep dive
Hack Time
After all the preliminaries are over it was finally time to start hacking.
Hackers formed teams, large and small.
The competition for the best vest was fierce:

They staked out a comfortable workspace in chairs …
Or on the floor …
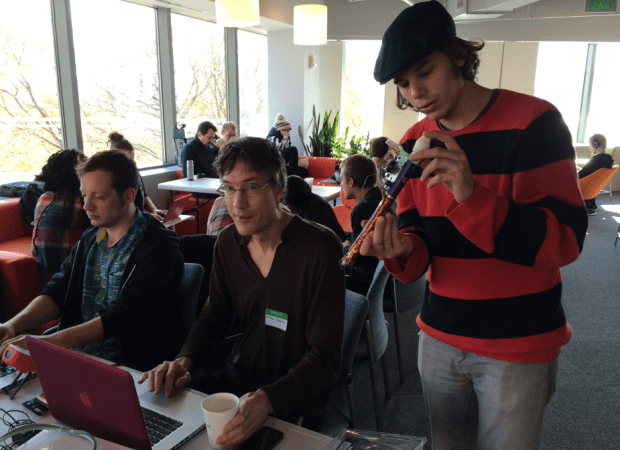
There were some very creative hardware hacks:

Software hacks:

Plenty of good food

And lots of fun


Overnight Hacking

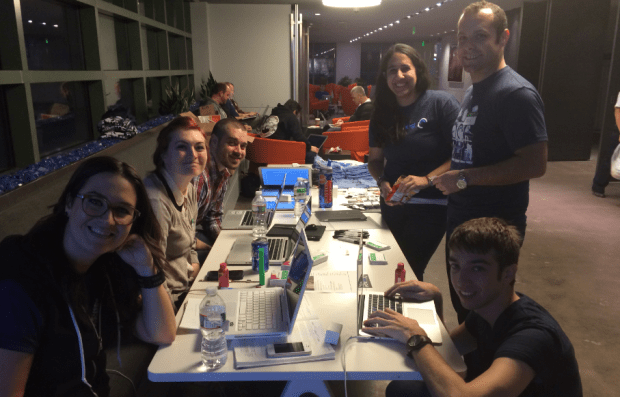
The Microsoft NERD was only available until 9PM – after that we moved over to hack/reduce – a wonderful hacking space a five minute walk away. There we were greeted by a perfect hacking space with lots of great wifi, great hacker lighting, and lots of beer. Hacking continued all night. Some hackers did try to get some sleep (either at the hack, or back at home), but some hardcore hackers stayed the whole night.
By 9AM on Sunday morning, the hackers were back at the NERD, for lots of coffee, some breakfast and then more hacking.
Hacking ends
At 2:30, hacking was officially over, and teams submitted their projects to Hacker League. Sixty hacks were submitted.
Demo Session
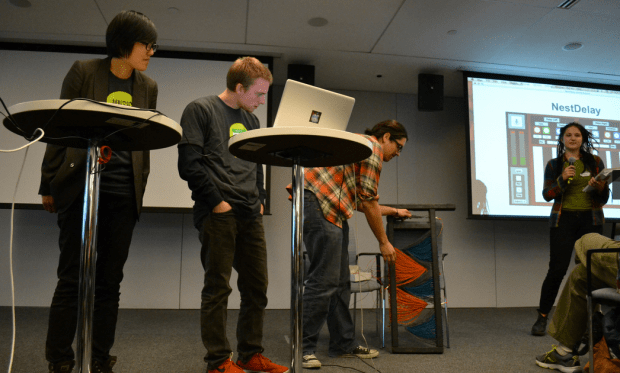
By 3PM the 200 hackers had all gathered back into the big room joined by a hundred folks who had come just to see the demo session. Hackers had two minutes to show their stuff. It is a hard demo to give. You are giving a demo of software that you’ve just finished building. It might have some bugs. The WiFi is a little flaky, you haven’t slept in 24 hours, your hands are shaking from too much coffee and too much nervousness, you have to type while holding a microphone and your laptop just won’t sync with the projector just right, and the audio isn’t coming out of the speakers, and the colors look all wrong on the screen. All in front of 300 people. I’ve done it dozens of times and it still is a really scary demo to give. But it is incredibly exhilarating too – to take nothing but an idea and turn it into something that can amaze or amuse a room full of tech elite in 24 hours. It is quite a rush.

Here I am giving my demo, heart pounding, blood racing …
There were two A/V setups so while one team was presenting, the next team was setting up. This allowed us to get through 60 demos in just over two hours. There was a very low incidence of demo fail. And only two inappropriate demos (one was a 2 minute powerpoint presentation with no tech built, the other was a 2 minute tech commercial for a product). I was worried that we might have a #titstare moment with one hack that seemed to contain questionable content but that hacker apparently decided not to present.
The 60 hacks represented a wide range of domains. There were games, music learning tools, programs designed to create, manipulate, remix and even destroy music. I’d love to cover them all, but there are just too many.
The full list is on hacker league. Here are some of my absolute favorites:
String Theory – A musical instrument and sound sculpture build from yearn and stretch sensors and powered by an Arduino.
String Theory
The Lone Arranger – a terminal app that allows you to easily rearrange your audio. By a father and son hacking team.

The Secret History of Music – combs biographies, lyrics, and commentary from song meanings from two artists, combines them into one fictional artist, and uses Markov chain magic to generate a 50K novel about this new fictional band.
LED Soundsystem – this hack attempts to generate a light show synchronized to the music. It has a special place in my heart because the hacking team was working on the same problem I was working on for my abandoned hack – i.e. automatically finding the ‘drop’ in a song. Unfortunately, this team had a demo fail – but they are smart guys and I expect to see good stuff from them at the next hack day.

eHarmonica – an electronic harmonica!
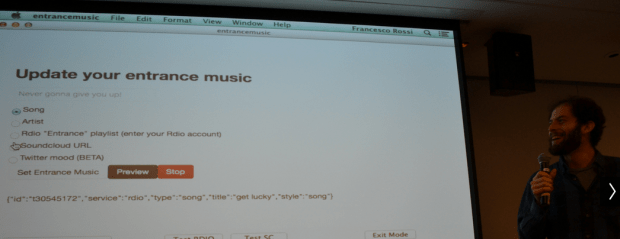
Enter the dragon – In today’s world, everyone deserves a spectacular entrance. And we intend to give it to them. Enter the Dragon uses bluetooth technology to detect when a user enters the room and plays their personalized entrance music.
Dadabots – Dadabots are bot accounts on creative websites that make procedural creations or remixes of other creations
ios SoundPuzzle – A simple iOS ear training game built programmatically from the free music archive and the echonest remix api.
danceomatic – totally awesome automatic choreography from an mp3 and a web based stick figure performance.
Jotunnslayer – Never again listen to power metal without slaying ice giants. Die in battle. Earn your place in Valhalla.
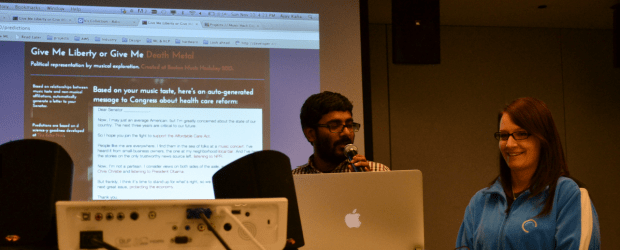
Give Me Liberty or Give Me Death Metal – Political representation via musical exploration
Echos – Choose your favorite song and shoot to the beat! Fight enemies that respond to and are controlled by the music! Listen closely and experience unparalleled power as you get into the groove! Enjoy addictive arcade-style game-play in this twist on a classic formula.
TweetTones – a native iOS application that generates synthesized music from tweets in real-time.

Short-Attention Span Playlist Scanner – Glenn made a radio scanner that find and plays just the choruses.

ionian Eclipse – A web-based multiplayer top-down space shooter with procedurally generated enemies and interactions driven by music events.
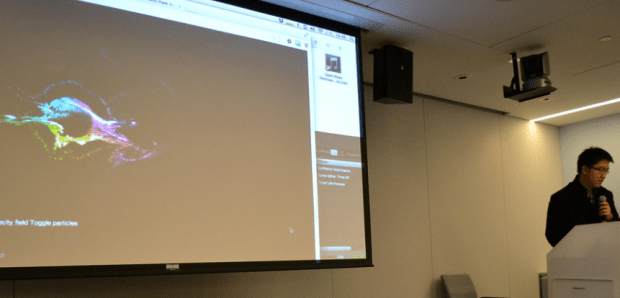
CFD is Colorful Fluid Dynamics: A HTML5 Music Visualizer and Spotify Plugin – A music visualizer written entirely in vanilla javascript/canvas that is based on computational fluid dynamics and a complex particle system.
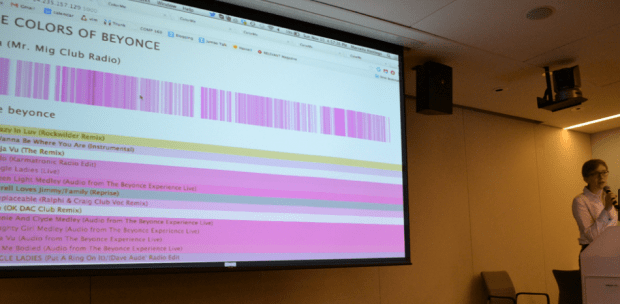
ColorMe – Ever wondered what your music looked like? Now you can look at songs by your favorite artist with this super fun web app, powered by the Echo Nest.
How Repetitive – measures how often audio segments repeat themselves within in a given song.

Jason’s music visualizer – an html/css visualizer on steroids.

And last, but by no means least, Jonathan’s awesome MIDI Digester that converts audio to MIDI and back, over and over to generate some very strange sounds. The very essence of the music.
There are so many excellent hacks, I’m sure I’ve missed many notables. Luckily, Evolver.fm covered the event, so expect to see Eliot’s writups on all the best hacks on Evolver.fm.
Prizes
At the end of the mega demo session, there’s a brief prize awarding ceremony where a half-dozen organizations give out modest prizes for hackers that made cool stuff using their tech.
Finally we adjourned to the local pub for some food, beer and hacking recaps.

Special thanks to the organizers of the event. The Music Hack Day would not happen without Elissa and Matt. They do all the hard work. Finding the venue, wrangling the sponsors and volunteers, making a mega Costco food run, dealing with the A/V, running the registration, selecting and hiring the caterers, designing t-shirts and so much more. There’s a huge amount of work that goes into planning the event, much more than meets the eye. Elissa and Matt are the unsung heroes of Music Hack Day. We should make a music hack to sing their song.
Thanks also to the event sponsors: Rdio, Spotify, Microsoft, hack/reduce, Free Music Archive, SoundCloud, Mailchimp and The Echo Nest, and the many volunteers who came and helped us run the whole show.
Some of the awesome and unusually attractive volunteers at Music Hack Day Boston
More Music Hack Days
Interested in going to a Music Hack Day? Check out the Music Hack Day calendar for upcoming events. There’s one in Helsinki this weekend, and there’s one in London in just a few weeks. More events are rumored to be in the planning stages for 2014.
(Photos mostly by Michelle Ackerman, a few by me)
The Ultimate List of Music APIs
Posted by Paul in code, Music, The Echo Nest, web services on October 24, 2013
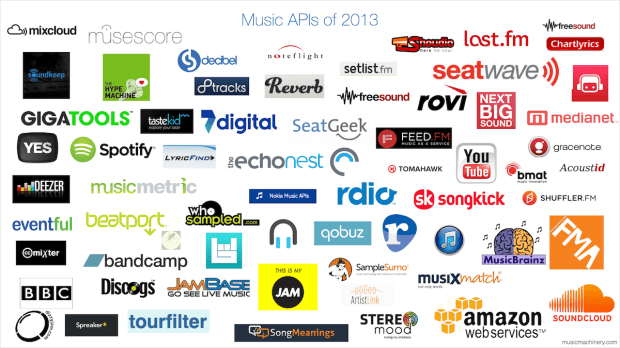
I’ve started to build the ultimate list of music APIs. My goal for the list is for it to be a one-stop spot to find the best music apis. Currently 65 APIs are listed across 10 categories. Check out the list here: Music APIs
The Fighting Fifth – The Fifth Harmony fan army
Posted by Paul in data, Music, recommendation on September 13, 2013
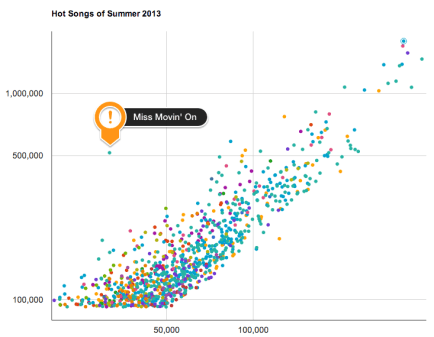
In yesterday’s post about the Hot Songs of Summer 2013, I noted that some songs were attracting a very passionate fan base. In particular, the song Miss Movin’ On by Fifth Harmony was an extreme outlier, attracting more than twice the number of plays per listener than any other song.
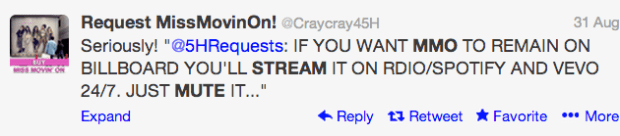
Based on this data I suggested that the Fifth Harmony was going places – such high passion among their listeners was surely indicative of future success. But now I am not so sure. Shortly after I made that post I learned that our crack data team here at The Echo Nest were already on to some Fifth Harmony shenanigans. Yes, Fifth Harmony is getting lots of plays, but many of these plays are due to an orchestrated campaign. Fifth Harmony fans are encouraged to go to music streaming sites such as Spotify and Rdio and stream Miss Movin’ On (aka MMO) 24/7. Here are some examples:
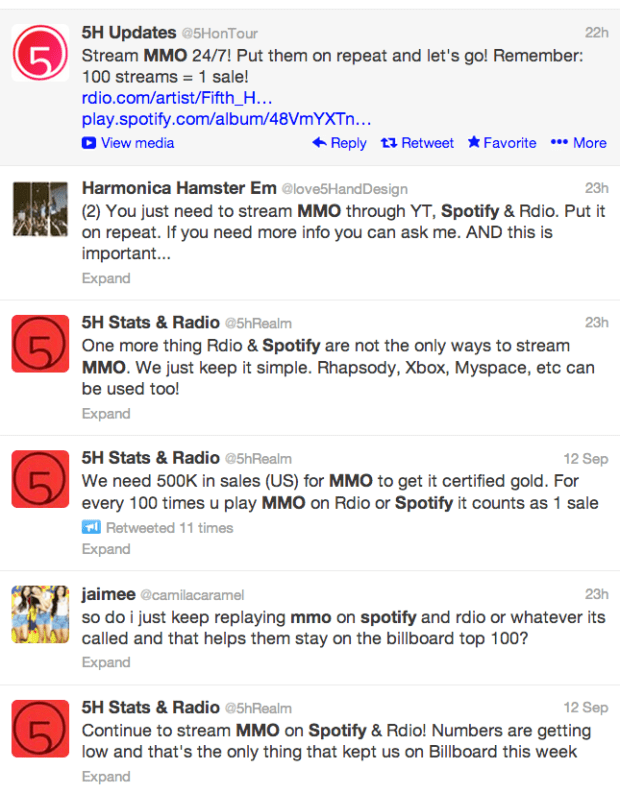

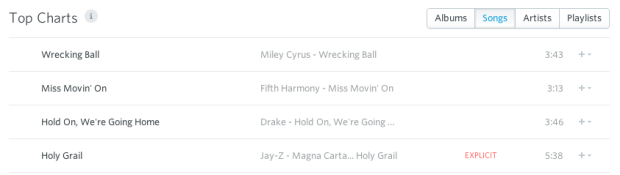
There are a number of twitter accounts that are prompting such MMO plays. The campaign seems to be working. 5H is moving up in the charts. Just take a look at the top songs on Rdio this week, Miss Movin’ On is number two on the list:
But what effect is this campaign really having on Fifth Harmony? Perhaps Fifth Harmony’s position on the charts is a natural outcome of their appeal, and is not a result of a small number of fans that stream MMO 24/7 with their computers and iPhones on mute. Can we see the effect that The Harmonizers are having? And if so, how substantial is this effect? The answer lies in the data, so that’s where we will go.
Can we see the effect of the Harmonizers?
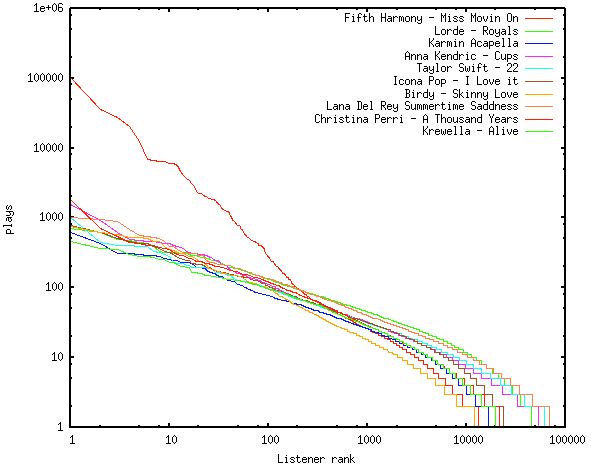
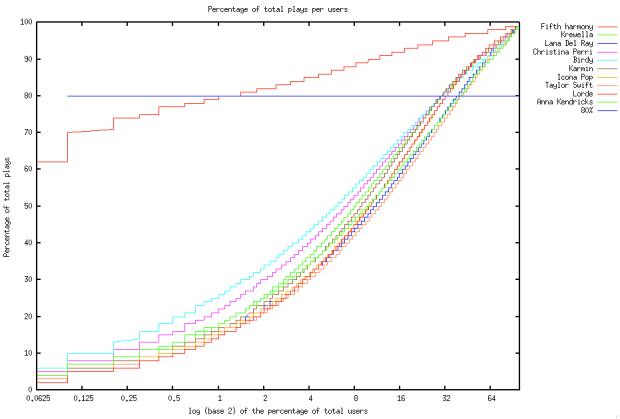
The first thing to do is to take a look at the listener play data for MMO and compare it to other songs to see if there are any tell-tale signs of a shilling campaign. To do this, I selected 9 other songs with similar number of fans that appeal to a similar demographic as MMO. For each of these songs I ordered the listeners in descending play order (i.e. the first listener is the listener that has played the song the most) and plotted the number of plays per listener for the 10 songs.
As you can see, 9 out of 10 songs follow a similar pattern. The top listeners of a song have around a thousand plays. As we get deeper into the listener ranks, the number of plays per listener drops off at a very predictable rate. The one exception is Fifth Harmony’s Miss Movin’ On. The effect of the Harmonizers is clearly seen. The top plays are skewed to greatly inflate the total number of plays by two full orders of magnitude. We can also see that the number of listeners that are significantly skewing the data is relatively small. Beyond the top 200 most active listeners (less than 0.5 % of the Fifth Harmony listeners in the sample), the listening pattern for MMO falls in line with the rest of the songs. It is pretty clear that the Harmonizers are really having an effect on the number of plays. It is also clear that we can automate the detection of such shilling by looking for such non-standard listening patterns.
Update – a reader has asked that I include One Direction’s Best Song Ever on the plot. You can find it here.
How big of an impact do the Harmonizers have on the overall play count?
The Harmonizers are having a huge impact. 80% of all track plays of Miss Movin’ On are concentrated into just the top 1% of listeners. Compare that to the other 9 tracks in our sample:
Percentage of listeners that account for 80% of all plays
| Fifth Harmony – Miss Movin’ On | 1.0 |
|---|---|
| Lorde – Royals | 14.0 |
| Karmin – Acapella | 16.0 |
| Anna Kendrick – Cups | 17.0 |
| Taylor Swift – 22 | 14.0 |
| Icona Pop – I love it | 15.0 |
| Birdy – Skinny Love | 25.0 |
| Lana Del Rey – Summertime Sadness | 15.0 |
| Christina Perri – A Thousand Years | 21.0 |
| Krewella – Alive | 17.0 |
A plot of this data makes the difference quite clear:
I estimate that at least 75% of all plays of Miss Movin’ On are overplays that are a direct result of the Harmonizer campaign.
What effect does the Fifth Harmony campaign have on chart position?
It is pretty easy to back out the overplays by finding another song that has a similarly-shaped plays vs listener rank curve once we get beyond past the first 1% of listeners (the ones that are overplaying the track). For instance, Karmin’s Acapella has a similar mid-tail and long-tail listener curve and has a similar audience size making it a good proxy. It’s Summer Time rank was 378. Based on this proxy, MMO’s real rank should be dropped from 45 to around 375. This means that a few hundred committed fans were able to move a song up more than 300 positions on the chart.
The bottom line here is that an organized campaign for very little cost has harnessed the most passionate fans to substantially bolster the apparent popularity of an artist, making the artist appear to be about 4 times more popular than it really is.
What does this all mean for music services?
Whenever there’s a high-stakes metric like chart position some people will try to find a way to game the system to get their stuff to the top of the chart. Twenty years ago, the only way to game the charts was either by spending lots of money buying copies of your record to boost the sales figures, or bribe radio DJs to play your songs to boost radio airplay. With today’s music subscription services, there’s a much easier way to game the system. Fans and shills need to simple play a song on autorepeat across a a few hundred accounts to boost the chart position of a song. Fifth Harmony proves that if you have a small, but committed fan base, you can radically boost your chart position for very little cost.
Obviously, a music service doesn’t like this. First, the music service has to pay for all those streams, even if no one is actually listening to them. Second, when a song gets to the top of a chart through shilling and promotion campaigns, it reduces the listening enjoyment for those who use the charts to find music. Instead of finding a new song that got to the top of the chart based solely (or at least mostly) on merit, they are listening to a song that is a product of a promotion machine. Finally, music services that rely on user play data to generate music recommendations via collaborative filtering have a significant problem trying to make sure that fake plays don’t improperly influence their recommendations.
So what can be done to limit the damage to music services? As we’ve seen, it is pretty easy to detect when a song is being overplayed via a campaign and these overplays can be removed. Perhaps even simpler though is to rely on metrics that are less easily gamed – such as the number of fans a song has instead of the total number of plays. For a music subscription service that has a credit card number associated with each user account, the number of fans a song has is a much harder metric to hack.
What does this say about Fifth Harmony fans ?
I am always happy when I see people getting excited about music. The Fifth Harmony fans are really excited about Miss Movin’ On, the tour and the upcoming album. Its great that the fans are so invested in the music that they want to help the band be successful. That’s what being a fan is all about. But I hope they’ll avoid trying to take their band to the top by a shortcut. As they say, it’s a long way to the top if you want to rock n’ roll. Let Fifth Harmony earn their position at the top of charts, don’t give them a free ride.
And finally, a special message to music labels or promoters: If you are trying to game the music charts by enlisting hundreds of pre-teens and teens to continuously stream your one song: screw you.
Update – I’ve received **lots** of feedback from Harmonizers – thanks. A common theme among this feedback is that the fan activities and organization really are a grassroots movement, and there really is no input from the labels. Many took umbrage with my suspicions that the label was pulling the strings. I remain suspicious, but less so than before. My parting ‘screw you’ comment was in no way directed at the 5H fans, it was reserved for the mythical music label marketeer who I imagined was pulling the strings. I’m hoping to dig in a bit deeper to understand the machinery behind the 5H fan movement. Expect a follow up article soon.
The Saddest Stylophone – my #wowhack2 hack
Posted by Paul in hacking, Music, The Echo Nest on August 15, 2013
Last week, I ventured to Gothenburg Sweden to participate in the Way Out West Hack 2 – a music-oriented hackathon associated with the Way Out West Music Festival.

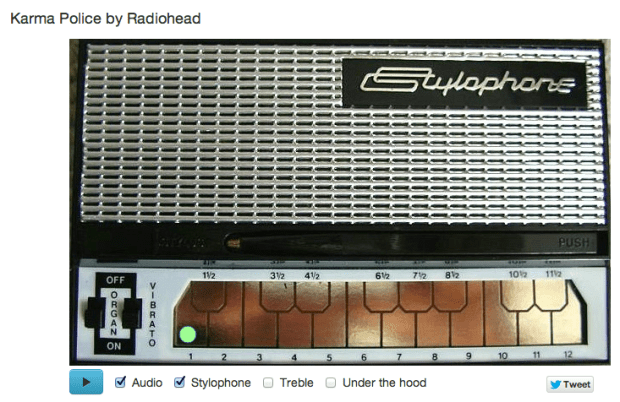
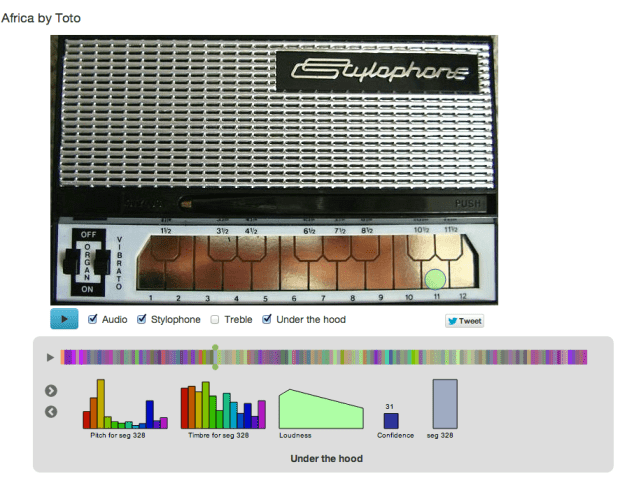
I was, of course, representing and supporting The Echo Nest API during the hack, but I also put together my own Echo Nest-based hack: The Saddest Stylophone. The hack creates an auto accompaniment for just about any song played on the Stylophone – an analog synthesizer toy created in the 60s that you play with a stylus.

Two hacking pivots on the way … The road to the Saddest Stylophone was by no means a straight line. In fact, when I arrived at #wowhack2 I had in mind a very different hack – but after the first hour at the hackathon it became clear that the WIFI at the event was going to be sketchy at best, and it was going to be very slow going for any hack (including the hack I had planned) that was going to need zippy access to to the web, and so after an hour I shelved that idea for another hack day. The next idea was to see if I could use the Echo Nest analysis data to convert any song to an 8-bit chiptune version.  This is not new ground, Brian McFee had a go at this back at the 2012 MIT Music Hack Day. I thought it would be interesting to try a different approach and use an off-the-shelf 8bit software synth and the Echo Nest pitch data. My intention was to use a Javascript sound engine called jsfx to generate the audio. It seemed like it pretty straightforward way to create authentic 8bit sounds. In small doses jsfx worked great, but when I started to create sequences of overlapping sounds my browser would crash. Every time. After spending a few hours trying to figure out a way to get jsfx to work reliably, I had to abandon jsfx. It just wasn’t designed to generate lots of short overlapping and simultaneous sounds, and so I spent some time looking for another synthesizer. I finally settled on timbre.js. Timbre.js seemed like a fully featured synth. Anyone with a Csound background
This is not new ground, Brian McFee had a go at this back at the 2012 MIT Music Hack Day. I thought it would be interesting to try a different approach and use an off-the-shelf 8bit software synth and the Echo Nest pitch data. My intention was to use a Javascript sound engine called jsfx to generate the audio. It seemed like it pretty straightforward way to create authentic 8bit sounds. In small doses jsfx worked great, but when I started to create sequences of overlapping sounds my browser would crash. Every time. After spending a few hours trying to figure out a way to get jsfx to work reliably, I had to abandon jsfx. It just wasn’t designed to generate lots of short overlapping and simultaneous sounds, and so I spent some time looking for another synthesizer. I finally settled on timbre.js. Timbre.js seemed like a fully featured synth. Anyone with a Csound background would be comfortable with creating sounds with Timbre.js It did not take long before I was generating tones that were tracking the melody and chord changes of a song. My plan was to create a set of tone generators, and dynamically control the dynamics envelope based upon the Echo Nest segment data. This is when I hit my next roadblock. The timbre.js docs are pretty good, but I just couldn’t find out how to dynamically adjust parameters such as the ADSR table. I’m sure there’s a way to do it, but when there’s only 12 hours left in a 24 hour hackathon, the two hours spent looking through JS library source seemed like forever, and I began to think that I’d not figure out how to get fine grained control over the synth. I was pretty happy with how well I was able to track a song and play along with it, but without ADSR control or even simple control over dynamics the output sounded pretty crappy. In fact I hadn’t heard anything that sounded so bad since I heard @skattyadz
would be comfortable with creating sounds with Timbre.js It did not take long before I was generating tones that were tracking the melody and chord changes of a song. My plan was to create a set of tone generators, and dynamically control the dynamics envelope based upon the Echo Nest segment data. This is when I hit my next roadblock. The timbre.js docs are pretty good, but I just couldn’t find out how to dynamically adjust parameters such as the ADSR table. I’m sure there’s a way to do it, but when there’s only 12 hours left in a 24 hour hackathon, the two hours spent looking through JS library source seemed like forever, and I began to think that I’d not figure out how to get fine grained control over the synth. I was pretty happy with how well I was able to track a song and play along with it, but without ADSR control or even simple control over dynamics the output sounded pretty crappy. In fact I hadn’t heard anything that sounded so bad since I heard @skattyadz  play a tune on his Stylophone at the Midem Music Hack Day earlier this year. That thought turned out to be the best observation I had during the hackathon. I could hide all of my troubles trying to get a good sounding output by declaring that my hack was a Stylophone simulator. Just like a Stylophone, my app would not be capable of playing multiple tones at once, it would not have complex changes in dynamics, it would only have a one and half octave range, it would not even have a pleasing tone. All I’d need to do would be to convincingly track a melody or harmonic line in a song and I’d be successful. And so, after my third pivot, I finally had a hack that I felt I’d be able to finish in time for the demo session and not embarrass myself. I was quite pleased with the results.
play a tune on his Stylophone at the Midem Music Hack Day earlier this year. That thought turned out to be the best observation I had during the hackathon. I could hide all of my troubles trying to get a good sounding output by declaring that my hack was a Stylophone simulator. Just like a Stylophone, my app would not be capable of playing multiple tones at once, it would not have complex changes in dynamics, it would only have a one and half octave range, it would not even have a pleasing tone. All I’d need to do would be to convincingly track a melody or harmonic line in a song and I’d be successful. And so, after my third pivot, I finally had a hack that I felt I’d be able to finish in time for the demo session and not embarrass myself. I was quite pleased with the results.
How does it work? The Sad Stylophone takes advantage of the Echo Nest detailed analysis. The analysis provides detailed information about a song. It includes information about where all the bars and beats are, and includes a very detailed map of the segments of a song. Segments are typically small, somewhat homogenous audio snippets in a song, corresponding to musical events (like a strummed chord on the guitar or a brass hit from the band).
A single segment contains detailed information on the pitch, timbre, loudness. For pitch it contains a vector of 12 floating point values that correspond to the amount of energy at each of the notes in the 12-note western scale. Here’s a graphic representation of a single segment:
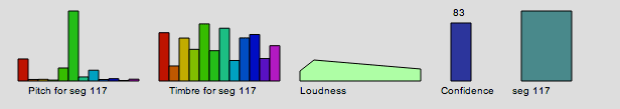
This graphic shows the pitch vector, the timbre vector, the loudness, confidence and duration of a segment.
The Saddest Stylophone only uses the pitch, duration and confidence data from each segment. First, it filters segments to combine short, low confidence segments with higher confidence segments. Next it filters out segments that don’t have a predominant frequency component in the pitch vector. Then for each surviving segment, it picks the strongest of the 12 pitch bins and maps that pitch to a note on the Stylophone. Since the Stylophone supports an octave and a half (20 notes), we need to map 12 notes onto 20 notes. We do this by unfolding the 12 bins by reducing inter-note jumps to less than half an octave when possible. For example, if between segment one and segment two we would jump 8 notes higher, we instead check to see if it would be possible to jump to 4 notes lower instead (which would be an octave lower than segment two) while still remaining within the Stylophone range. If so, we replace the upward long jump with the downward, shorter jump. The result of this a list of notes and timings mapped on to the 20 notes of the Stylophone. We then map the note onto the proper frequency and key position – the rest is just playing the note via timbre.js at the proper time in sync with the original audio track and animating the stylus using Raphael.
I’ve upgraded the app to include an Under the hood selection that, when clicked opens up a visualization that shows the detailed info for a segment, so you can follow along and see how each segment is mapped onto a note. You can interact with visualization, stepping through the segments, and auditioning and visualizing them.
That’t the story of the Saddest Stylophone – it was not the hack I thought I was going to make when I got to #wowhack – but I was pleased with the result, when The Sad Stylophone plays well, it really can make any song sound sadder and more pathetic. Its a win. I’m not the only one – wired.co.uk listed it as one of the five best hacks at the hackathon.
Give it a try at Saddest Stylophone.
MIDEM Hack Day recap
What better way to spend a weekend on the French Riviera then in a conference room filled with food, soda, coffee and fellow coders and designers hacking on music! That’s what I and 26 other hackers did at the MIDEM Music Hack Day. Hackers came from all over the world to attend and participate in this 3rd annual hacking event to show what kind of of creative output can flow from those that are passionate about music and technology.
Unlike a typical Music Hack Day, this hack day has very limited space so only those with hardcore hacking cred were invited to attend. Hackers were from a wide range of companies and organizations including SoundCloud, Songkick, Gracenote, Musecore, We Make Awesome Sh.t, 7Digital, Reactify, Seevl, Webdoc, MuseCore, REEA, MTG-UPF, and Mint Digital and The Echo Nest. Several of the hackers were independent. The event was organized by Martyn Davies of Hacks & Bants along with help from the MIDEM organizers.
The hacker space provided for us is at the top of the Palais – which is the heart of MIDEM and Cannes. The hacking space has a terrace that overlooks the city, giving an excellent place to unwind and meditate while trying to figure out how to make something work.
The hack day started off with a presentation by Martyn explaining what a Music Hack Day is for the general MIDEM crowd. After which, members of the audience (the Emilys and Amelies) offered some hacking ideas in case any of the hyper-creative hackers attending the Hack Day were not able to come up with their own ideas.
After that, hacking started in force. Coders and designers paired up, hacking designs were sketched and github repositories were pulled and pushed.
The MIDEM Hack Day is longer than your usual Music Hack Day. Instead of the usual 24 hours, hackers have 45 hour to create their stuff. The extra time really makes a difference (especially if you hack like you only have 24 hours).
We had a few visitors during the course of the weekend. Perhaps the most notable was Robert Scoble. We gave him a few demos. My impression (based upon 3 minutes of interaction, so it is quite solid), is that Robert doesn’t care too much about music. (While I was giving him a demo of a very early version of Girl Talk in a Box, Robert reached out and hit the volume down key a few times on my computer. The effrontery of it all!). A number of developers gave Robert demos of their in-progress hacks, including Ben Fields, who at the time, didn’t know he was talking to someone who was Internet-famous.
As day turned to evening, the view from our terrace got more exciting. The NRJ Awards show takes place in the Palais and we had an awesome view of the red carpet. For 5 hours, the sounds of screaming teenagers lining the red carpet added to our hacking soundtrack. Carly Rae, Taylor Swift, One Direction and the great one (Psy) all came down the red carpet below us, adding excitement (and quite a bit of distraction) to the hack.
[youtube http://www.youtube.com/watch?v=OUkLAsphZDM]Yes, Psy did the horsey dance for us. Life is complete.
Finally, after 45 hours of hacking, we were ready to give our demos to the MIDEM audience.
There were 18 hacks created during the weekend. Check out the full list of hacks. Some of my favorites were:
- VidSwapper by Ben Fields. – swaps the audio from one video into another, syncronizing with video hit points along the way.
- RockStar by Pierre-loic Doulcet – RockStar let you direct a rockstar Band using Gesture.
- Miri by Aaron Randal – Miri is a personal assistant, controlled by voice, that specialises in answering music-related questions
- Ephemeral Playback by Alastair Porter – Ephemeral Playback takes the idea of slow music and slows it down even further. Only one song is active at a time. After you have listened to it you must share it to another user via twitter. Once you have shared it you can no longer listen to it.
- Music Collective by the Reactify team – A collaborative music game focussing on the phenomenon of how many people, when working together, form a collective ‘hive mind’.
- Leap Mix by Adam Howard – Control audio tracks with your hands.
It was fun demoing my own hack: Girl Talk in a Box – it is not everyday that a 50 something guy gets to pretend he’s Skrillex in front of a room full of music industry insiders.
All in all, it was a great event. Thanks to Martyn and MIDEM for making us hackers feel welcome at this event. MIDEM is an interesting place, where lots of music business happens. It is rather interesting for us hacker-types to see how this other world lives. No doubt, thanks to MIDEM Music Hack Day synergies were leveraged, silos were toppled, and ARPUs were maximized. Looking forward to next year!
Boil the Frog – the unreleased Spotify Version
Update – You are probably looking for this web-based version of Boil The Frog and the blog post about it.
The rest of this article is about the unreleased Spotify Version of Boil the Frog.

I’m at Music Apps Hack Weekend doing my favorite thing: hacking on music. I’ve just finished my hack called Boil the Frog. Boil the Frog is a Spotify App that will create playlists that gradually take you from one music style to another. It is like the proverbial story of the frog in the pot of water. If you heat the water gradually, the frog won’t notice and will happily sit in the pot until it becomes frog stew. With Boil the Frog you can do the same thing musically. Create a playlist that gradually takes your pre-teen from Miley Cyrus to Miles Davis, or perhaps more perversely the Kenny G fan to Cannibal Corpse.
To build the app I built an artist similarity graph of 100,000 of the most popular artists. I use The Echo Nest artist similarity to connect each artist to its four nearest neighbors. To find the path between any two artists I use a bidirectional Dijkstra shortest path algorithm. Most paths can be computed in less than 100ms.
The Spotify Apps API is the perfect hacking platform. You can build a Spotify app that has full access to the vast Spotify music catalog and artwork, along with access to the listener’s catalog. Since the Spotify Apps run in an embedded browser all of your web app programming skills apply. You can use jQuery, make calls to JSON APIs, use HTML 5 canvas. It is all there. Spotify has done a really good job putting together this platform. The only downside is that, unlike the web, it is hard to actually release Spotify apps, but the Spotify team is working to make this easier. I’d love to release Boil the Frog because it is really fun to make playlists that bring you from one music style to another. It is interesting to see what musical neighborhoods you wander through on your way. For instance, I made a Kenny G to Cannibal Corpse playlist. To get there, the playlist brought me from easy listening, to movie soundtracks and then through video game soundtracks to get to the heavy metal world. Cool stuff. If you want to see a playlist between two artists let me know in the comments and I’ll create and share the playlist with you.
I made a video of Boil the Frog in action. Check it out:
[youtube http://youtu.be/Nj6JAxm9aPE]
Update: I’ve just pushed the client code out to github: https://github.com/plamere/boilthefrog
Hardware hacking at Music Hack Day Boston
There will be some opportunities for organized hardware hacking at this weekend’s Music Hack Day Boston in the form of afternoon workshops. All the details are on the Music Hack Day Workshops page. Here’s just a teaser to wet your appetite.
Electric Eels Workshop by Noah Vawter with Justin from Burnkit 2600. This project introduces a mobile platform for melodic and percussive electronic music instruments. It encourages playing them more like traditional instruments- electrical energy is produced on a note-by-note basis from its players’ movements.
Atari Punk Console Workshop – Jimmie Rodgers will lead a workshop on building Atari Punk Consoles. The Atari Punk Console is a simple synthesizer with a wide range of sounds. It is so named because the sounds generated are similar to those of the early Atari consoles.
Pen Plotter & Chiplotle workshop – While not exactly hardware hacking, it is definitely old school. Douglas Repetto and Brian Whitman will show you how to plot your beautiful music visualizations or whatever else on quite possibly the sexiest of all paper output mechanisms — early 1980s HPGL pen plotters!

The sexiest of all paper output mechanisms
Programmable Audio Effects in a Sketch Environment with LeafLabs’ Maple – by Okie Williams. In this 2 hour workshop you will learn how you can use Maple with a little extra circuitry (op-amps, resistors, capacitors) to program your own audio effects in an Arduino-like sketch environment and focus mainly on programming effects instead of hardware.
When 4Chan Gamed the Time 100
Last week I did a skype interview with a reporter from Time who was interested in the backstory on how the 2009 Time 100 Poll was hacked. They’ve put it all together into a nifty video segment: When 4Chan gamed the TIME 100
TechCrunch rickrolls the Hype Machine
Posted by Paul in Music, recommendation on July 12, 2009
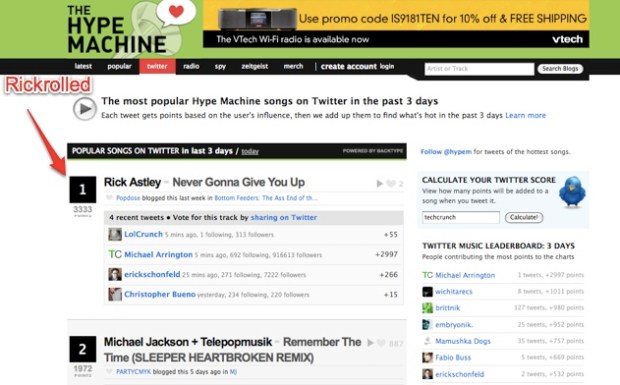
Last week, on the Hype machine blog, Anthony indicated his increasing frustration in how easily charts could be manipulated – Anthony wanted a better way, one that was transparent, and gave more influence to the influential. Anthony’s solution was to create a twitter chart that is based on the twittering activity of Hype Machine songs. In this new chart Twitterers with more followers have more influence than those with few.
A number of commenters on Anthony’s blog pointed out how it would be easy for a single very popular twitter user to influence the charts. And that is exactly what Erick Schonfeld of TechCrunch did. Erick used the power of TechCrunch for evil.
With one tweet from the TechCrunch twitter account (with its nearly 1 million-person reach) he was able to put Rick Astley’s Never Gonna Give you Up at the top of the Hype Machine Twitter chart. Erick writes “The Hype Machine’s formula is flawed. No single person should be able to affect the rankings so easily“.
It’s arguable whether or not this is a dishonest manipulation of the charts. TechCrunch really does have a reach of 1 million people – and so by tweeting Rick Astley they are potentially exposing those millions to this song. However, in reality, people don’t read TechCrunch for music recommendations – TechCruch is just not a music tastemaker (sorry Erick). A tweet by TechCrunch counts much less than a tweet by Indie music guide Pitchfork.
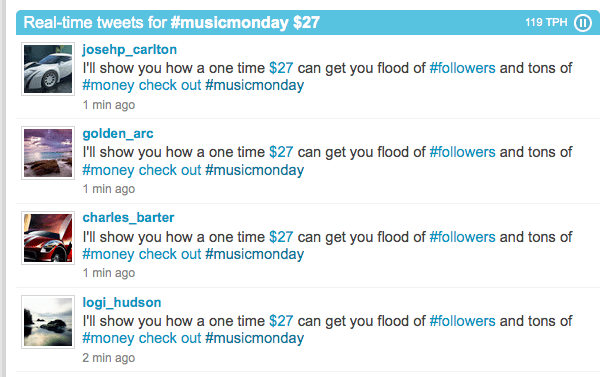
Update – Note that the spammers are now starting to recognize the twitterverse as a place that they can target. If you have $27 you can get the twittertrafficmachine to get you 20K followers in a month:
Anthony should adjust how he scores a tweet to not only include the reach of the tweet but to also include the music reputation of the source. It is not as easy to determine the music reputation as the number of followers for a source, but it is much more important. Some indicators that a tweet has real influences are whether people actually click on the link and listen to the song and whether the poster actually listens to music, especially new music, before it gets popular.
I suspect Anthony will be tweaking his scoring algorithms soon to make the charts better reflect what real music listeners are listening to, not just what popular people are listening to.
Update: Anthony has responded in he comments.
The Shill Machine
Posted by Paul in Music, recommendation on June 30, 2009
 The very popular blog aggregator The Hype Machine has a ‘Popular Page‘ that shows the tracks that have been most favorited in the last 3 days. This is a great way to find out what the music zeitgeist is. However, Anthony (Mr. Hype Machine) recently discovered that a number of highly favorited artists seemed to have reached the popular page by nefarious means. According to Anthony, it appears that a number of artists became popular when many presumably fake accounts, created from the same IP address in a very short period of time all favorited a single artist in an apparent effort to get the artist to appear on the popular page. This type of hacking is not too surprising – whenever you have a chart or poll that relies on ‘the wisdom of crowds’ you are susceptible to the shill who will try to manipulate the chart in order to promote their interests. We see this in online polls, social news sites and popular music sites.
The very popular blog aggregator The Hype Machine has a ‘Popular Page‘ that shows the tracks that have been most favorited in the last 3 days. This is a great way to find out what the music zeitgeist is. However, Anthony (Mr. Hype Machine) recently discovered that a number of highly favorited artists seemed to have reached the popular page by nefarious means. According to Anthony, it appears that a number of artists became popular when many presumably fake accounts, created from the same IP address in a very short period of time all favorited a single artist in an apparent effort to get the artist to appear on the popular page. This type of hacking is not too surprising – whenever you have a chart or poll that relies on ‘the wisdom of crowds’ you are susceptible to the shill who will try to manipulate the chart in order to promote their interests. We see this in online polls, social news sites and popular music sites.
When Anthony became aware of how the Hype Machine was being manipulated, he and the rest of the Hype machine team fought back, instituting a Captcha mechanism to prevent automated account creation, ignoring favoriting activity for new accounts, and keeping a much closer eye on new account activity.
But Anthony didn’t stop there, he went one step further. He named names. He posted on his blog a list of all the artists that, according to Anthony have “attempted to manipulate the charts on the Hype Machine”. Anthony says he published the list to “let everyone make their own judgments about quality, integrity and marketing strategies:”. But really, I suspect that Anthony’s real motivation was to shame those that would attempt to try to enlist the Hype Machine to promote their band.
A commenter on that blog post that claims membership in one of the outed shilling bands protests that they absolutely did not create fake accounts and they had been unfairly defamed (literally) by the Hype Machine. But Anthony responds with a list 4 tracks by the band that had each been favorited from a single IP address by over 40 separate, newly created accounts. Anthony says “Given that this is a time-consuming activity that primarily benefits you, you can see how it appears likely that you or your team may have been involved”.
Should Anthony have outed these artists? Surely the excessive favoriting could have been an overzealous fan that decided to try out a new way to hype their favorite band (to put the ‘hype’ in Hype Machine, if you will), and the band is blameless. But from Anthony’s point of view it doesn’t really matter. Anthony is going to protect the integrity of the Hype Machine and he’s going to do it by pointing to any band that has benefited from ‘unnatural’ enthusiasm. Even if it means public humiliation for the blameless.
I suspect Anthony’s next problem will occur when some pranksters realize that they can get any band blacklisted at the Hype Machine by a bit of nefarious activity. By simply creating a set of sham accounts and favoriting tracks by the vicitim band from those sham acounts, the Hype Machine can be manipulated into blacklisting and humilating the band. Is your ex-girlfriend’s new boyfriend in a band? Get your dorm floor to create 50 Hype Machine accounts, favorite his tracks and watch the fun as he gets outed and shamed as a shill.
The lesson here is that charts that show popularity are hard to get right – they can be easily manipulated for fun or for profit. Anthony should be prepared to fight an escalating war against those that want to manipulate his charts. And the more popular the Hype Machine becomes, the bigger the target it will be for the hackers and the shills.